Products
A comprehensive suite of SaaS products tailored to simplify your business operations with cost-effective ROI
Cygnet Tax
Transform tax processes to ensure compliance
Cygnet Vendor Post Box
Automate end-to-end vendor management
Cygnet IRP
Approved Invoice Registration Portal by GSTN
Cygnet Bills
Cloud based billing solution to generate bills, e-Invoices and e-Way bills
Cygnature
Cloud-based digital & electronic signing solution
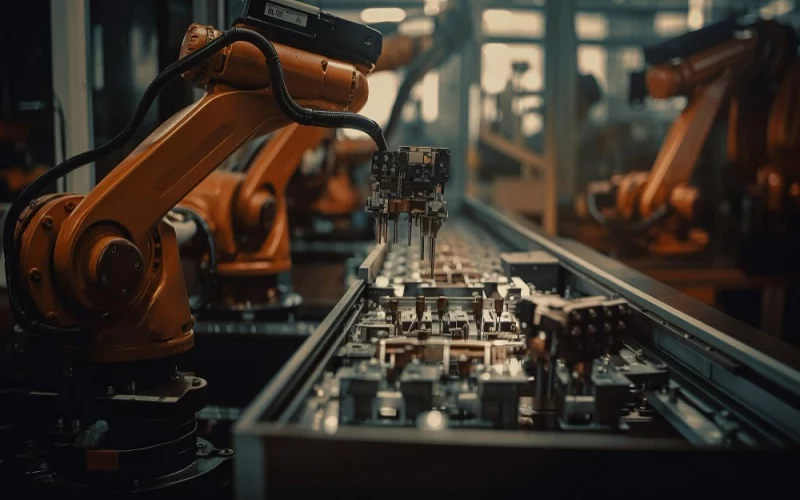
Automationwhiz
Automate business processes with RPA bots
TestingWhiz
Low code no code test automation tool
Cygnet Finalyze
Data-driven platform enabling real-time assessment for BFSI
Cygnet Origin
Onboarding journey for seamless experience
Services
Lead the digital transformation spectrum with Cygnet technology services
Digital Engineering
Revolutionizing enterprises with technology excellence
Quality Engineering
Elevate your standards with our precision-driven quality engineering
Enterprise Applications & SAP
Revolutionize your enterprise with our SAP and application solutions
Data, Analytics, AI/ML
Unleash the power of data with our analytics and AI/ML expertise
Security as a Service
Secure your operations with our robust Security as a Service
Solutions
Explore a diverse portfolio of comprehensive solutions crafted to enhance your business process transformation.
Accounts Payable
Enhance vendor relations by streamlining AP
GL Reconciliation
Streamline day-to-day GL reconciliation processes
Litigation Management
Introducing AI-Powered Notice Response Solutions
Source to Pay
Bring unparalleled efficiency to your S2P journey
Intelligent Document Processing
Template agnostic data extraction and processing with AI-OCR
One Stop Destination for
Indirect tax compliance
Transforming architectures with AI capabilities
Coalition of domain, integration and technical expertise
Client's complex legacy solutions modernization
Scalable infrastructure with 99% uptime
Client Satisfaction Rate
Scalable infrastructure with 99% uptime
Referral Based Business
Client's complex legacy solutions modernization
Over half a Billion e-invoices generated through Cygnet’s Platform
Clients Speak
Dive into the tapestry of experiences shared by those who walked the journey with us
Cygnet COSMOS
Digital Transformation Framework for Immersive Experience
Co-Ideate
Co-Ideate for new product development & new market GTM
1 Industry-First Approach
Co-Create
Co-Create technology enabled connected business solutions
2 Speed to Value
Co-Innovate
Co-Innovate intelligent solutions with Cygnet Launchpad
3 Value Based Method
Co-Evolve
Co-Evolve with a strong continuum of Cygnetians, Clients & Partners
4 Evolve Together
At Cygnet, we are driven by our commitment to Living the Trust, embodying our strong heritage and core values.

Resources
The more you engage, the better you will realize our role in the digital
transformation journey of your business